Cybersecurity firm Threat Fabric says it has found a new family of mobile-device malware that can launch a fake overlay for certain apps to trick Android users into providing their crypto seed phrases as it takes over the device.
Threat Fabric analysts said in a March 28 report that the Crocodilus malware uses a screen overlay warning users to back up their crypto wallet key by a specific deadline or risk losing access.
“Once a victim provides a password from the application, the overlay will display a message: Back up your wallet key in the settings within 12 hours. Otherwise, the app will be reset, and you may lose access to your wallet,” Threat Fabric said.
“This social engineering trick guides the victim to navigate to their seed phrase wallet key, allowing Crocodilus to harvest the text using its accessibility logger.”

Source: Threat Fabric
Once the threat actors have the seed phrase, they can seize complete control of the wallet and “drain it completely.”
Threat Fabric says despite it being a new malware, Crocodilus has all the features of modern banking malware, with overlay attacks, advanced data harvesting through screen capture of sensitive information such as passwords and remote access to take control of the infected device.
Initial infection occurs by inadvertently downloading the malware in other software that bypasses Android 13 and security protections, according to Threat Fabric.
Once installed, Crocodilus requests accessibility service to be enabled, which enables the hackers to gain access to the device.
“Once granted, the malware connects to the command-and-control (C2) server to receive instructions, including the list of target applications and the overlays to be used,” Threat Fabric said.
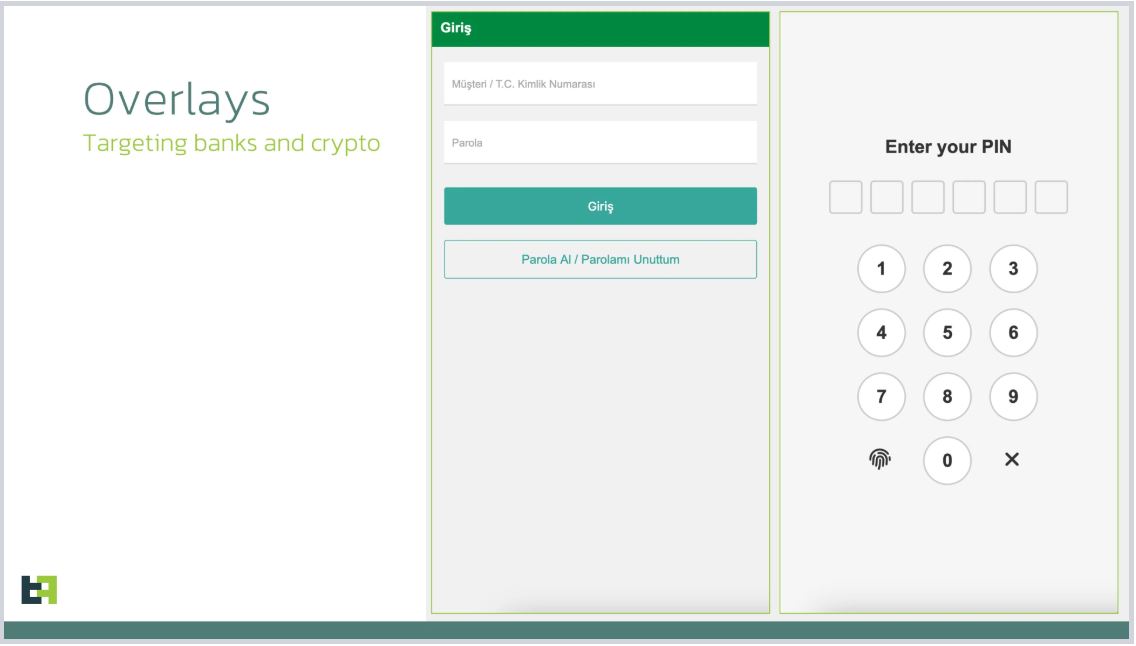
Once installed, Crocodilus requests accessibility service to be enabled, granting hackers access to the device. Source: Threat Fabric
It runs continuously, monitoring app launches and displaying overlays to intercept credentials. When a targeted banking or cryptocurrency app is opened, the fake overlay launches over the top and mutes the sound while the hackers take control of the device.
“With stolen PII and credentials, threat actors can take full control of a victim’s device using built-in remote access, completing fraudulent transactions without detection,” Threat Fabric said.
Threat Fabrix’s Mobile Threat Intelligence team has found the malware targets users in Turkey and Spain but said the scope of use will likely broaden over time.
Related: Beware of ‘cracked’ TradingView — it’s a crypto-stealing trojan
They also speculate the developers could speak Turkish, based on the notes in the code, and added that a threat actor known as Sybra or another hacker testing out new software could be behind the malware.
“The emergence of the Crocodilus mobile banking Trojan marks a significant escalation in the sophistication and threat level posed by modern malware.”
“With its advanced Device-Takeover capabilities, remote control features, and the deployment of black overlay attacks from its earliest iterations, Crocodilus demonstrates a level of maturity uncommon in newly discovered threats,” Threat Fabric added.
Magazine: Ridiculous ‘Chinese Mint’ crypto scam, Japan dives into stablecoins: Asia Express